All Blogs
How to Choose a Vulnerability Scanner: Tips & Top Free Tools

Quick Summary: Looking for a vulnerability scanning tool? Choosing the right tool can be difficult with so many options out there. You need to consider many factors like coverage, accuracy, speed, and more. We will provide useful tips in this article that will help you pick the right vulnerability scanner. Keep reading for an informed decision making.
Vulnerabilities are a major risk factor for businesses today, irrespective of size. Considering the facts, even Verizon’s DBIR report finds that in 16% of data breach incidents, common vulnerabilities were the reason. It clearly shows they are the biggest threat to your data security and integrity.
Here comes the role of a vulnerability scanner or vulnerability assessment tool. It helps you discover security weaknesses in your web apps, APIs, and other digital assets. It conducts thorough security testing and detects a wide range of vulnerabilities.
Choosing the right tool for vulnerability assessment is a critical step in detecting and remediating vulnerabilities. A good vulnerability scanning tool will offer quality scanning, accurate results, and ease of testing. But how to choose a good vulnerability scanner? In this article, we will find an answer to this question. Keep reading to make the right choice.
Perform Deep Vulnerability Scanning and Uncover Hidden Risks Precisely with ZeroThreat Let’s Scan
On This Page
- Why is a Vulnerability Scanner Important?
- Tips to Choose a Vulnerability Scanner
- Top Vulnerability Assessment Tools
- What Type of Vulnerability Scanner Do You Need?
- Mistakes to Avoid in Choosing Vulnerability Scanner
- To Wrap Up
Why is a Vulnerability Scanner Important?
Vulnerability scanning is a crucial step in cybersecurity that aims to identify, prevent, and mitigate potential security risks. While it can be done manually, using a vulnerability scanner can minimize the effort and time involved in it. The scanner can help you uncover hidden weaknesses in your web apps, APIs, and other digital assets just like a magic wand. Let’s understand how it can help you with the benefits below.
- Automated Scanning: Automation helps you scan web apps, APIs, and other digital assets without human intervention. It helps to find security weaknesses more easily and quickly than manual testing. For example, according to CVE data, more than 38,500 vulnerabilities were found in the previous year. So, manually testing your digital assets for vulnerabilities will be a herculean task.
- Wide Range of Vulnerabilities: Vulnerability detection tools can help you identify different varieties of vulnerabilities. Some tools can even detect emerging vulnerabilities by analyzing application or system behavior.
- Prioritized Results: Priority-based results are sorted according to the severity of vulnerabilities. So, you can quickly identify vulnerabilities that are critical from a security point of view.
- Save Time: You can minimize the time and effort put into scanning your digital assets for vulnerabilities by automating the process with a tool. While manual security testing can take hours or days, automated scanning can do it in minutes.
Tips to Choose a Vulnerability Scanner
Since security testing is a critical process to ensure the integrity and safety of data, choosing the right vulnerability assessment tool is vital. Therefore, you must carefully choose it, as deploying the wrong tool can adversely affect your security posture. The following tips will play a crucial role in your decision-making. These tips can help you determine which is the best vulnerability scanner.
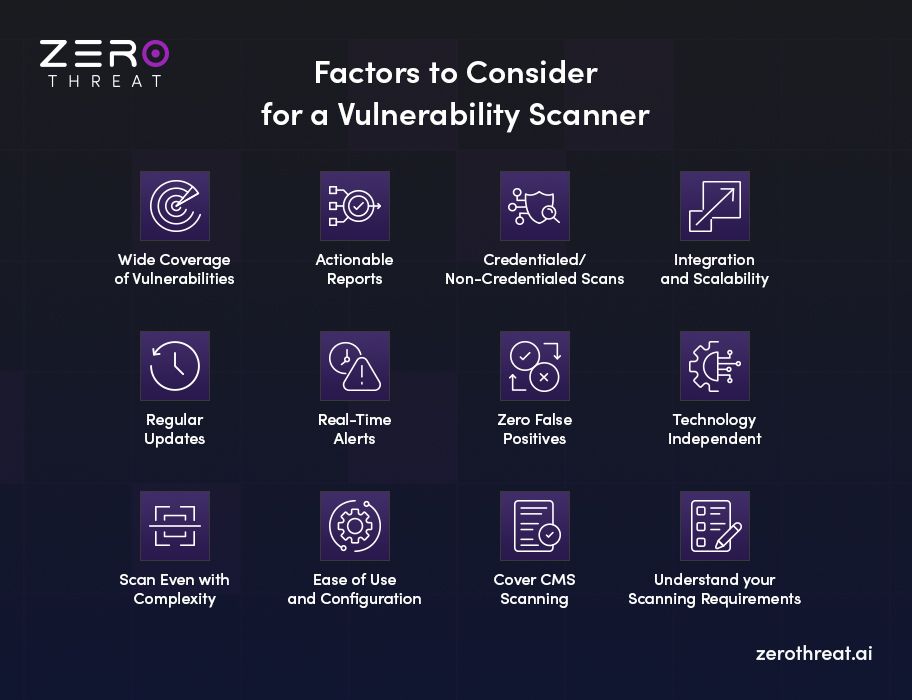
Wide Coverage of Vulnerabilities
Today, vulnerabilities are found in different varieties and severity levels. So, you cannot rely on tools that detect only common vulnerabilities and exposures, like OWASP Top 10 and CWE-25. Look for a vulnerability assessment solution that can also detect other vulnerabilities like out-of-band, zero-day, and 1-day exploits.
Actionable Reports
After scanning, you get a report that provides information on what kind of vulnerabilities are detected and their associated severity. However, a good vulnerability scanning tool will provide more accurate, detailed, and actionable insights. Plus, it will present this data in an easy-to-understand format. It can show you compliance issues and severity levels like critical, low, or moderate. Many tools even provide suggestions on how to resolve security issues.
Just a Scan Can Help You Avoid Cybersecurity Incidents by Identifying Weak Spots Try It for Free
Credentialed/Non-Credentialed Scans
Non-credentialed scanning helps discover common vulnerabilities in publicly available pages and resources on your web application. On the other hand, credentialed scanning helps uncover deep-rooted vulnerabilities by also scanning pages and resources protected behind logins.
Credentialed or authenticated scanning requires user authentication during vulnerability scanning to assess protected pages and resources. Your business should prefer a cybersecurity vulnerability assessment tool that covers both kinds of testing for broader vulnerability coverage.
Integration and Scalability
Seamless integration of a vulnerability scanner with your existing security tools helps manage the process efficiently. Additionally, the tool should be adaptable to your evolving business needs to ensure optimal security testing within a growing digital ecosystem. Hence, check for scalability and integration characteristics when choosing a vulnerability scanner.
Regular Updates
Timely updates enable a vulnerability scanning tool to efficiently identify and report security weaknesses. This also ensures an up-to-date database of vulnerabilities to detect emerging risks precisely. Hence, you should look for a scanner that is updated in a timely manner and has a database that is actively maintained.
Real-Time Alerts
Many security vulnerability assessment tools offer continuous scanning, providing real-time threat alerts when they are detected. You can choose such a tool for continuous security testing of APIs, applications, and systems. Besides scheduling vulnerability scans, it is a plus that allows you to set up automated scans at regular intervals for optimal cybersecurity.
Zero False Positives
When selecting a vulnerability scanner tool, checking for the rate of false positives is also important. Think of it as a false alarm or false detection. It means a scanner detects a vulnerability while it doesn’t actually exist. It is a problem that can result in wasted time and resources. You should choose a vulnerability detection tool that offers zero false positives or at least the lowest false positives.
Technology Independent
Today, there is a wide range of technologies used to build web apps, APIs, websites, and other digital assets. For example, a web application can be built using JavaScript, Python, .NET, Angular, and other technologies. Only the types of vulnerability scanners that are not dependent on technology can help scan assets built with different technologies. So, look for a tool that can scan digital assets regardless of the technology they are built on.
Scan Even with Complexity
Crawling a web application is a necessary step in vulnerability scans. In this process, all web app elements, like pages, forms, and more, are identified. However, as web applications are becoming more complex, scanning them requires advanced solutions. For example, applications making heavy use of JavaScript are hard to scan with an ordinary vulnerability scanner. However, good scanners can do this easily and discover security weaknesses accurately.
Ease of Use and Configuration
For many users, the best vulnerability scanner is one that offers a seamless user interface. Indeed, ease of use is a critical factor in selecting a vulnerability scanning tool. It will help you spend most of your time in fixing vulnerabilities, instead of understanding how the tool works.
Besides this, easy configuration is another important factor to consider when selecting a vulnerability scanning tool. There are many tools that require no configuration and many that require only a few configuration steps.
Cover CMS Scanning
Organizations often use content management systems (CMSs) to manage their websites. Some popular CMSs include WordPress, Drupal, and Joomla. If you are using a CMS, you can choose a vulnerability scanning tool that supports CMS scanning.
Understand Your Scanning Requirements
You need to understand what kind of vulnerability scanner will fit your requirements. There are different types of vulnerability scanners. For example, web app scanners, network scanners, host-based scanners, and more. Each of them offers some unique features to identify vulnerabilities for the respective digital asset. So, define your requirement and choose the one that fits your need.
Ensure Complete Data Protection with a Thorough Vulnerability Assessment Start Now
Top Vulnerability Assessment Tools for Businesses
There are many popular vulnerability scanners available in the market today and they offer a wide range of features. You can use these scanners to discover vulnerabilities like OWASP top 10, CWE 25, and more. These tools are suitable for a variety of use cases and cybersecurity requirements. Many of these tools are free and some of them have both paid and free versions. Let’s check out these tools.
- ZeroThreat
- ZAP
- Nikto
- Burp Suite
- OpenVAS
- Nmap
- Nessus
- Acunetix
- Nexpose
Which Kind of Vulnerability Scanner is Suitable for You?
A vulnerability scanner, aka vulnerability assessment tool, is software designed to automate the tasks of identifying, prioritizing, and remediating security weaknesses in applications and systems. This tool plays a crucial role in your cybersecurity strategy, providing proactive measures to defend against risks.
Vulnerability assessment tools vary as per their usage, testing methodology, pricing, and other factors. So, it might be the case that a tool working fine for one organization may not work for the other. For instance, a basic vulnerability scanner is sufficient for small organizations and startups, but it won’t be suitable for a large organization with a wider and more complex infrastructure.
Although there are plenty of one-size-fits-all kinds of tools, it is essential to understand your requirements precisely to pick the best vulnerability assessment tool for your business. So, let’s consider the options based on your business’s requirements to make the right choice.
Check Your Budget
Vulnerability assessment tools for businesses are usually expensive, carrying a heavy price tag. Often these tools charge between $100 - $500 per scan. Now, this can be a costly deal for cash-strapped organizations, especially startups. So, they might prefer to choose a free vulnerability scanning tool. There are two options to choose from – free (usually open-source tools) and paid.
Understand the Methodology
Vulnerability scanners use different techniques to assess and discover vulnerabilities, as mentioned below.
- DAST (Dynamic Application Security Testing): DAST tools evaluate applications at runtime and perform simulated attacks to discover vulnerabilities.
- SAST (Static Application Security Testing): It analyzes the source code of an application to discover vulnerabilities.
- IAST (Interactive Application Security Testing): It uses both DAST and SAST techniques to discover vulnerabilities.
Depending on your requirements, you might choose one or two tools. For example, you can use a SAST tool during the development phase to actively identify and resolve vulnerabilities in coding. And use DAST during the testing phase to identify runtime vulnerabilities.
Type of Vulnerability Scanner
Your specific use case also plays an important role in choosing the right tool. There are different types of vulnerability scanners with varied scopes and usages, as mentioned below.
- Web application scanners
- Network scanners
- Port scanners
- Host-based scanners
- Database scanners
- Cloud scanners
Depending on your requirements, you can choose the right tool. For example, if you are looking for a web app vulnerability scanner, you can narrow down the choices and focus on tools that offer web app scanning.
Common Mistakes to Avoid When Choosing a Vulnerability Assessment Tool
You shouldn’t make a choice in a hurry, especially when it involves critical decisions like choosing a tool for security assessment. Yet, businesses make some mistakes in their choices. In this section, we are going to discuss some common mistakes that you should avoid when choosing a vulnerability assessment tool.
Focus More on Cost or Features
Avoid focusing solely on costs or features. You can end up picking a tool that is either expensive or basic. An expensive tool might be overbudgeted and a cheap one may lack quality and features. So, look for a balanced tool.
Mismatched Features
Often, businesses pick a tool that doesn’t align with their requirements in order to save costs. So, you must specify your requirements clearly and then look for options that match those needs.
Neglect Performance Impact
Advanced and continuous scanning comes at the cost of performance. So, you must carefully evaluate your choice to minimize the impact and ensure optimal scheduled scanning.
Miss All Quality Aspects
Don’t focus on a single quality aspect like wider scanning coverage or lower false positives. Look for a tool that offers high scanning quality with lower false positives and negatives, depth of scanning, better coverage, and clear reporting.
Missing Compliance Goals
Make sure that your vulnerability scanner offers features and reporting that align with your compliance goals.
To Wrap Up
As the threat landscape is growing, keeping your systems, applications, and other digital assets secure is becoming more challenging. Vulnerability scanning is a crucial step, and it should be done with the right tools and methods to achieve excellence.
You need a reliable tool like ZeroThreat which is a modern vulnerability scanner that offers 10X faster scanning, zero false positives, and reduces efforts in manual pen testing by 90%. Besides, it can scan JavaScript-heavy web apps and detect zero-day vulnerabilities.
Let’s try it for free and see more of its benefits.
Frequently Asked Questions
Which tool is good for scanning vulnerabilities?
A vulnerability scanner is good when it offers the lowest false positives, is not dependent on technology, scans complex applications, and more.
What are various types of vulnerability scanning tools?
What is the limitation of vulnerability scanners?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


